Ronin Hacker's Next Steps
What could be the hacker's next steps?
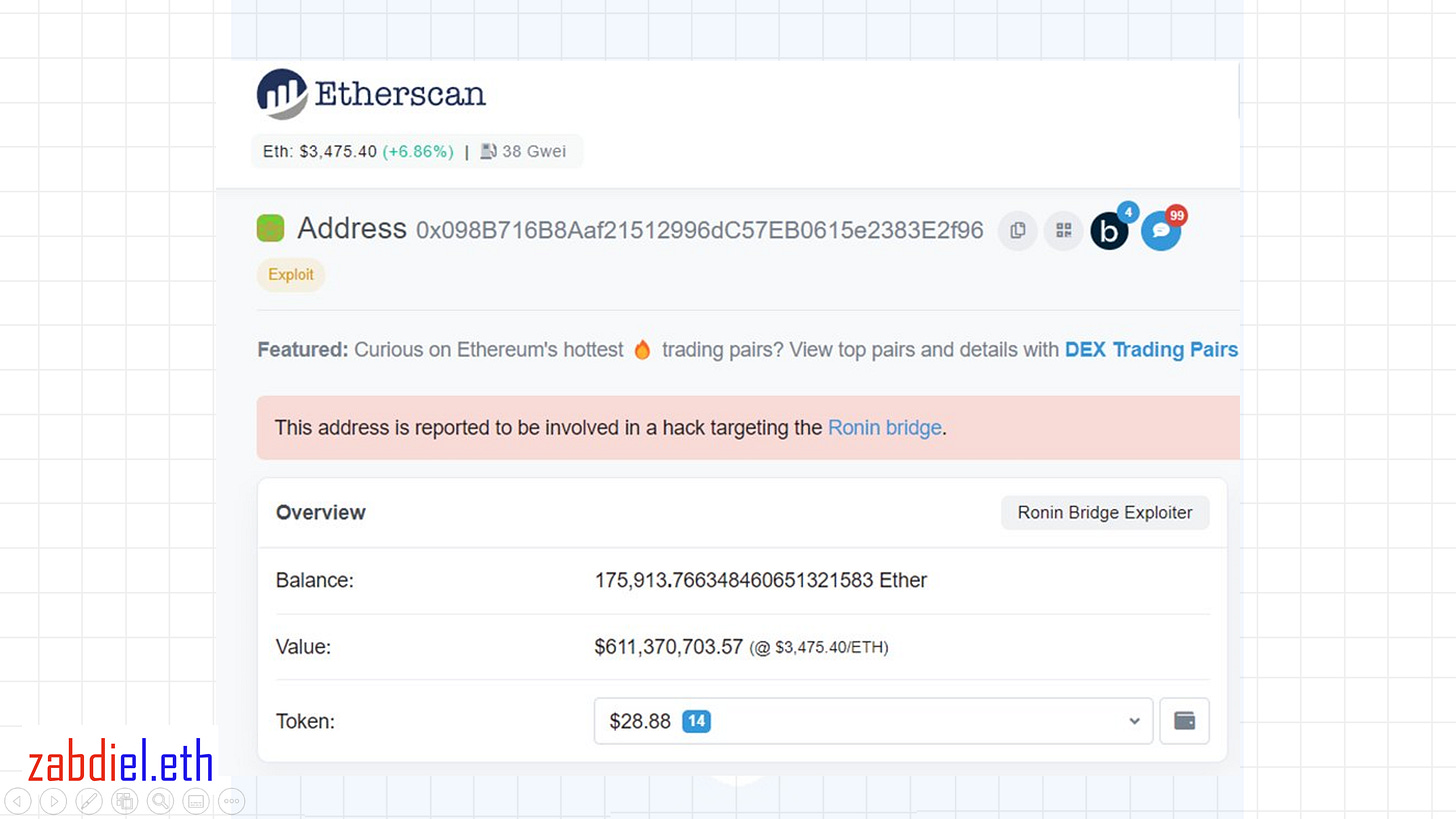
We discussed and detailed what happened in the recent Ronin hack in our last blog, and now we are here to examine the hacker's likely future steps, keeping in mind that the majority of the stolen assets are still sitting in the hacker's wallet.
As we all know, in order for that money to be more useful in this world, the hacker must convert those stolen assets into fiat currency, which will undoubtedly be a difficult task for the hacker. Or is it?
We all know that in order to convert our cryptocurrency assets into fiat currency, we must first register with a CEX, or centralized exchange, such as Binance, PDAX, Huobi, and others, and in order to do so, you must first go through their KYC, or Know Your Customer, procedures, which will require your personal information and documents.
So, without a doubt, the hacker will not resort to sending any funds to any CEX since a number of exchanges have already guaranteed their assistance in monitoring this wallet and its funds if any of the stolen funds are ever sent to their platforms.
The hacker's wallet could possibly be linked to a funding from CEX, which is easily traceable in the exchange data. Even if we assume that the hacker will use a hacked or fake account on an exchange, he will still have to deal with another issue because he will have to convert the funds sent to exchanges into fiat using banks, cards, and financial institutions, and even a dummy account that the hacker may use may still leave crumbs that could lead to their identity.
Other wallets that have interacted with the hacker's wallet may also be utilized to identify the hacker/s; as there is also a possibility that these linked wallets have interacted with a centralized exchange.
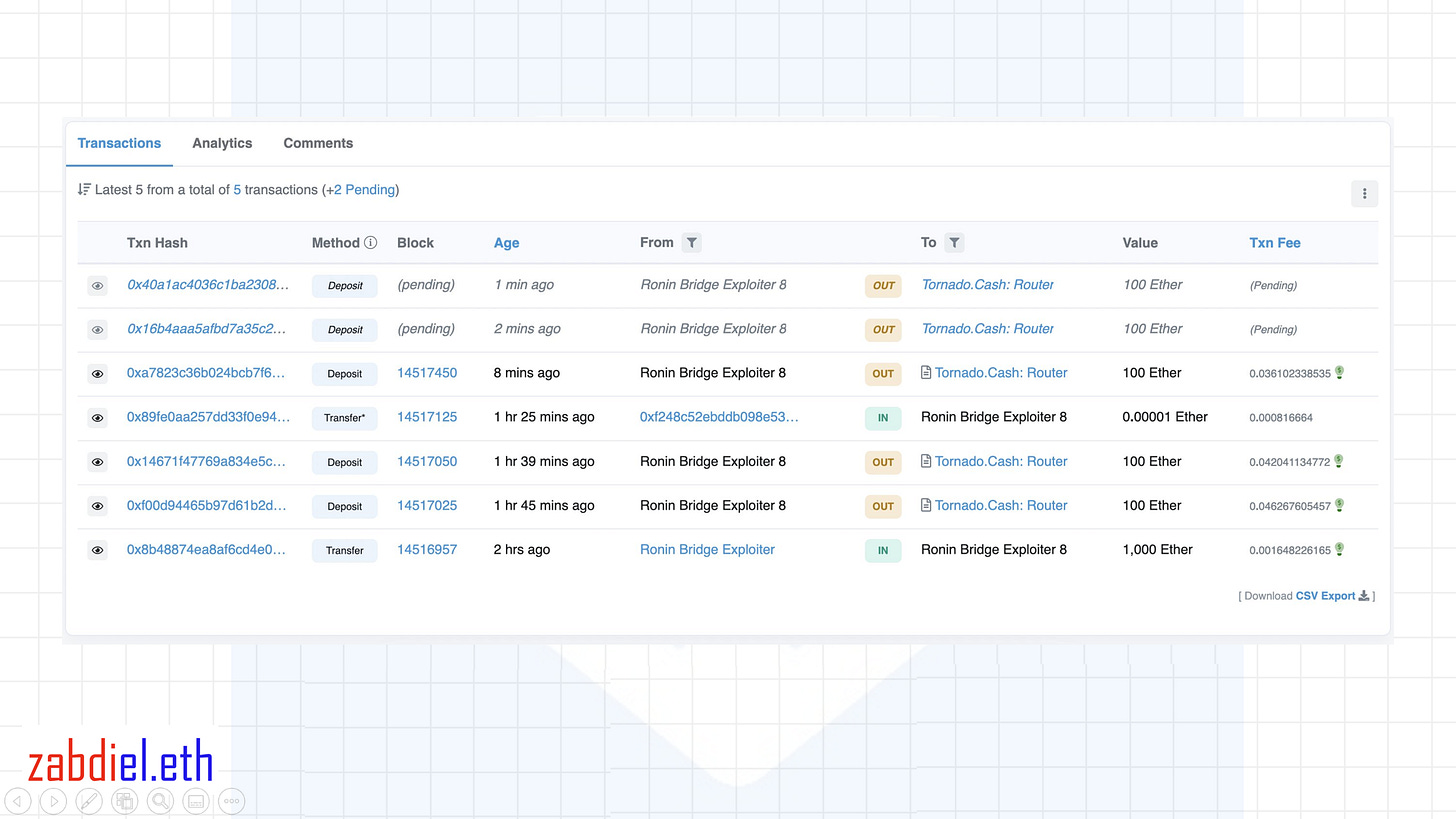
But, according to current news regarding the incident, the hacker is already using Tornado.cash and has sent some of the stolen ETH there. So, what exactly is Tornado.cash, and why is it being used by the hacker?
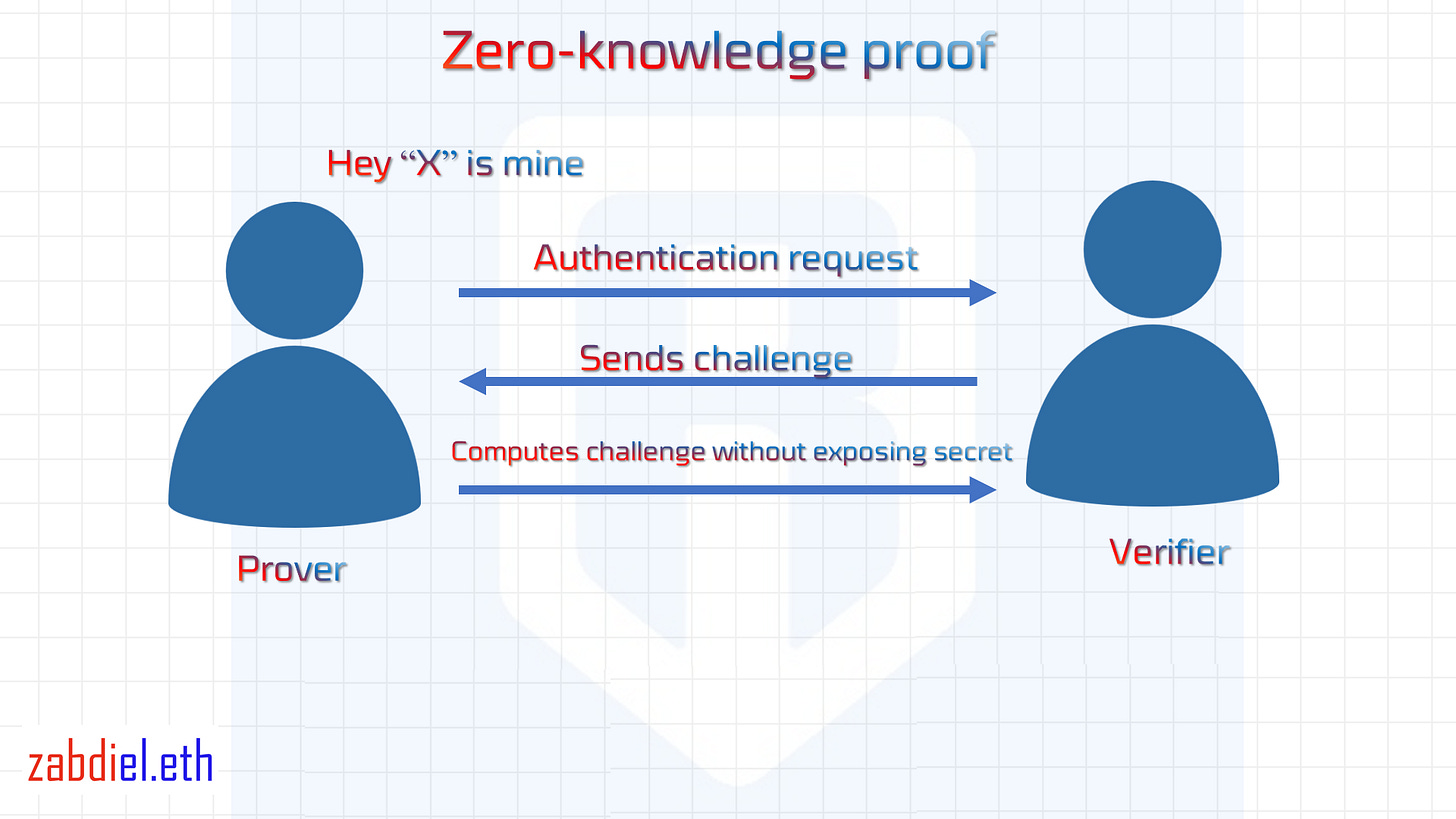
Tornado.cash is a decentralized protocol that uses ZK proofs. ZK proofs, also known as zero-knowledge proofs, are a means of authenticating something to a verifier without exposing why it is true. And the majority of ZK's applications are focused on cryptocurrencies, blockchain, and cryptography.
So ZK (ZK-snark) is used in the Tornado.cash protocol in such a way that the originating address proves to the protocol that it is the one who possesses the funds without giving any information that the funds originated at that address. Tornado Cash goal is to provide an additional layer of secrecy and anonymity in the space.
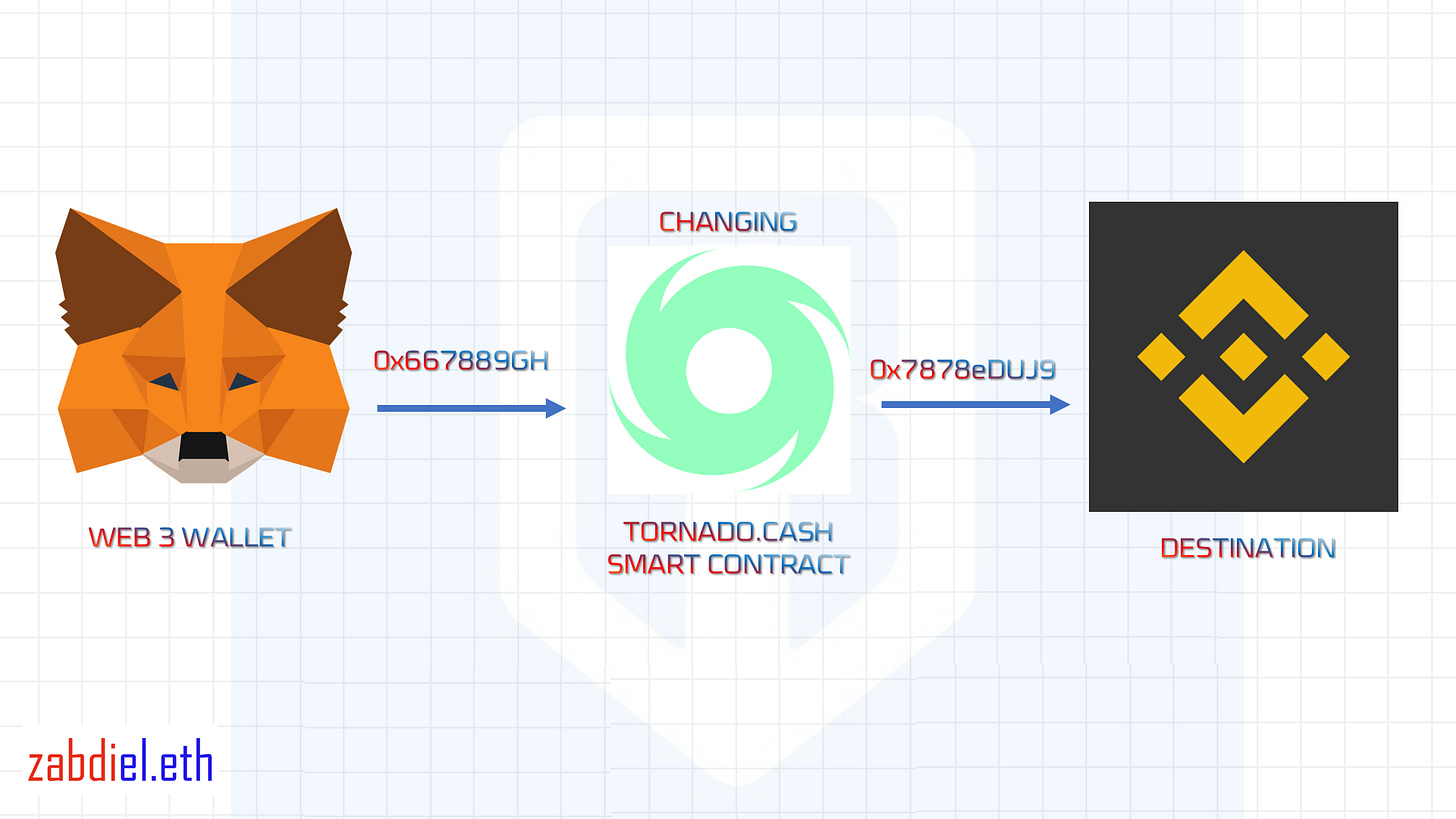
As a result, when a user sends an asset or cryptocurrency into the protocol, the smart contracts accept the token deposits from the originating address and withdraws it using a different address, and the receiver has no way of knowing where the funds originated because the address displayed in the explorer is the one provided by the smart contract.
As a result, when a user sends an asset or cryptocurrency into the protocol, the smart contracts accept the token deposits from the originating address and withdraws it using a different address, and the receiver has no way of knowing where the funds originated because the address displayed in the explorer is the one provided by the smart contract.
Why are the hacker/s using it?
Remember what we said about sending into Centralized Exchanges earlier? The hacker/s can use it in such a way that they can now send in assets without being caught because the address used in depositing will now be different and the exchange may have no means of knowing whether the money came from the hacker/s address and the hacker/s network of addresses.
Certainly, the funds will be moved little by little so that the transaction does not raise suspicion in the eyes of these exchanges and centralized financial institutions. However, CEX may still be able to screen assets entering their platforms and look for any traces that may lead them to the hacker or traces.
One thing I've learnt from this incident is that Web 2.0, or centralized institutions and platforms, is still crucial, especially as Web 3.0 emerges. There will undoubtedly be elements that must remain in Web 2.0 and others that are better suited to Web 3.0.
To conclude, it appears to us that the hacker/s do not have much space in the room to decide how to move the stolen funds. Either the hacker/s will risk getting caught making all of these movements, or they will return the stolen assets to the SkyMavis team. Only time will tell, and we don't know for sure. But we can be certain that the SkyMavis team and authorities are working hard to identify the individuals responsible for this breach.
Blog Link: https://zabdiel.eth.link/RoninHacker.html